Official statement
What you need to understand
What Is the Japanese Keyword Hack and Why Is It So Widespread?
The Japanese Keyword Hack is a particularly common hacking technique that involves massively injecting pages in Japanese or Chinese onto a compromised site. These pages often generate thousands of URLs containing commercial keywords to promote counterfeit or illegal products.
This attack typically exploits security vulnerabilities in outdated CMS platforms, non-updated plugins, or weak login credentials. The hackers' goal is to take advantage of the victim domain's authority to quickly rank their malicious pages.
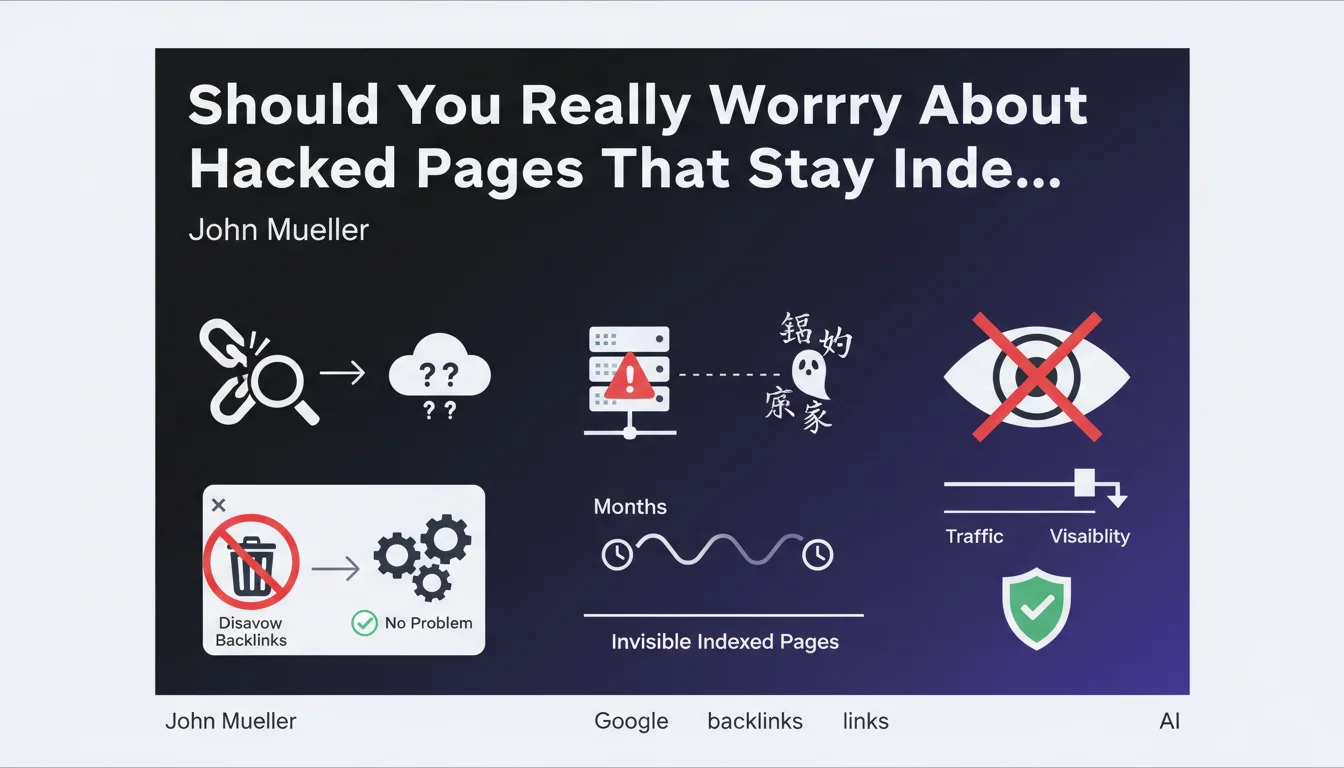
Why Does Google Claim These Indexed Pages Don't Pose a Problem?
John Mueller's statement specifies that old hacked pages can remain indexed for months without causing damage, provided they are not visited. This position is explained by the fact that Google understands the temporary nature of this content.
The search engine distinguishes between actively consulted pages and those that remain invisible in the index. As long as these URLs don't generate traffic and the site's visible content is healthy, the impact on overall SEO remains limited.
What Does "Invisible Indexed Pages" Actually Mean?
Invisible indexed pages are URLs present in Google's index but that don't appear in any relevant search results. They receive no organic traffic and don't participate in the site's ranking.
These pages end up being naturally deindexed over time, as Googlebot recrawls them and notices their disappearance or inaccessibility. The process can take several months depending on crawl frequency.
- Absolute priority: clean up visible content and secure the site
- Indexed but invisible hacked pages have a negligible SEO impact
- No need to disavow backlinks pointing to these temporary pages
- Prevent indexing of internal search results to avoid attack surfaces
- Natural deindexing takes time but happens automatically
SEO Expert opinion
Is This Approach Really Risk-Free for SEO?
John Mueller's recommendation is generally consistent with field observations, but it deserves some important nuances. Indeed, hacked pages that receive no traffic have a limited short-term SEO impact.
However, there are cases where a massive volume of poor-quality pages can affect crawl budget and the overall perception of site quality. If Googlebot spends its time crawling thousands of hacked pages, it will potentially neglect your legitimate content.
Additionally, certain indirect signals can play a role: if users accidentally land on these pages via brand searches and encounter malicious content, this can generate negative user experience signals.
When Should You Act Quickly on Deindexing Instead?
There are several situations where waiting for natural deindexing is not the best strategy. If hacked pages appear in brand search results or generate traffic, the urgency is maximum.
Similarly, if you notice a manual action from Google or a significant traffic drop correlated with the attack, you need to accelerate the deindexing process via Search Console. Using the URL removal tool then becomes relevant.
Is the Advice Not to Disavow Backlinks Always Valid?
Mueller's position on backlinks is pragmatic and justified in the majority of cases. Links pointing to temporarily hacked pages generally don't transmit a lasting negative signal to the main domain.
However, if you observe a particularly aggressive or toxic spam link pattern created specifically by hackers (PBN networks, massive over-optimized anchors), targeted disavowing may be justified. The analysis must be done case by case according to the link profile.
Practical impact and recommendations
What Should You Do Immediately After Detecting a Japanese Keyword Hack?
The first action is to completely secure the site: change all passwords, update the CMS and all plugins, identify and remove malicious files. Without this step, any cleanup action will be useless as the site will be reinfected.
Next, physically delete all visible hacked pages and verify that the URLs properly return 404 or 410 codes. Focus on pages that appear in search results or generate traffic.
For pages already indexed but invisible, let Google deindex them naturally. Use the URL removal tool in Search Console only for pages visible in SERPs, as this tool has limited capacity.
How Can You Effectively Prevent This Type of Attack?
Prevention requires rigorous security hygiene. Implement automatic updates for your CMS and extensions, use complex and unique passwords, enable two-factor authentication.
Install a reputable security plugin (Wordfence, Sucuri, iThemes Security for WordPress) and configure alerts to detect suspicious file modifications. Perform regular backups and store them off-server.
Block indexing of your internal search results via the robots.txt file and use meta noindex on pagination and filter pages to reduce the potential attack surface.
What Mistakes Should You Absolutely Avoid in Post-Hack Management?
Don't panic and don't use the URL removal tool excessively. This tool is limited to 1000 requests and should be reserved for truly problematic URLs that appear in search results.
Also avoid setting up 301 redirects from hacked pages to your homepage. This would potentially transfer negative signals and create a poor user experience. Prefer 404 or 410 codes.
- Immediately secure the site (passwords, updates, antimalware scan)
- Identify and physically remove all malicious files and content
- Verify that hacked pages return 404/410 codes
- Use the URL removal tool only for pages visible in SERPs
- Don't systematically disavow backlinks to these temporary pages
- Block indexing of internal search results (robots.txt + noindex)
- Implement security monitoring to detect reinfections
- Perform regular security audits (at least quarterly)
- Document the incident and corrective actions for future reference

💬 Comments (0)
Be the first to comment.